ipad visitor sign in app: A practical step-by-step guide
Learn how to use an ipad visitor sign in app safely, set up guest check-in, manage permissions, and log visits with a practical step-by-step guide.

You will learn how to set up and use an ipad visitor sign in app to greet guests, collect basic contact details, and issue temporary access. The guide covers choosing a sign-in app, configuring safety prompts, using QR codes or badges, and logging each visit for security records. Readers should have an iPad, Wi‑Fi, and admin access.
What is an ipad visitor sign in app?
An ipad visitor sign in app is a software solution that runs on an iPad to manage guest check-ins at reception, events, or offices. It guides visitors through a digital form, captures basic details, prints or emails badges, and logs each entry for security audits. The Tablet Info team highlights how such apps can streamline front-desk workflows, reduce paper clutter, and improve incident response times. When selecting a solution, look for privacy controls, ease of use, and compatibility with your existing access systems. This approach helps organizations maintain a clear, auditable record of who is in the building and when.
In practice, these apps replace paper sign-in books with a digital workflow that visitors can complete in minutes. They also enable hosts to approve or deny access quickly, while security teams can pull logs for audits. Proper configuration matters just as much as features, so this guide dives into practical steps and considerations for a smooth rollout.
Why this matters for facilities and security
Facilities teams bear responsibility for visitor safety and data privacy. A well-implemented ipad visitor sign in app reduces bottlenecks at the front desk, improves data accuracy, and creates a verifiable trail of entries. It supports compliance by collecting only what is necessary, storing records securely, and providing roles-based access to sensitive information.
Beyond security benefits, a digital check-in system enhances guest experience. Visitors can sign in quickly, receive temporary badges or QR codes, and be directed to their hosts without delays. For organizations with multiple locations, centralized logs enable easier reporting and cross-site visibility, while offline mode ensures the process works even when Wi-Fi is spotty.
Key features to look for
- Intuitive guest form with essential fields (name, host, contact, purpose, time-in/out)
- Optional badge printing or QR-code generation for quick access
- Roles-based permissions for staff, hosts, and admins
- Real-time logs with export options (CSV, JSON)
- Data minimization controls and retention settings
- Offline mode support and secure sync when online
- Integration hooks with access control systems or calendar apps
- Compliance-friendly prompts and consent options
Choosing a platform with these capabilities helps you balance speed, security, and privacy while delivering a smooth visitor experience.
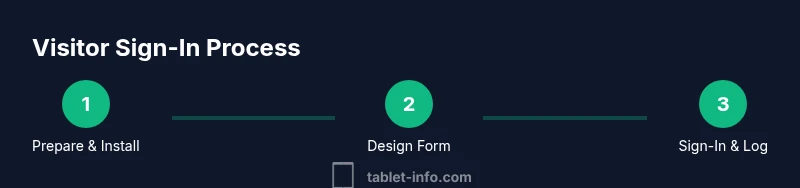
Step-by-step setup: preparing your iPad
Before you install anything, gather the essentials and prepare the iPad for a clean rollout. Charge the device fully and update to the latest iPadOS supported by your organization. Verify that you have a stable Wi-Fi connection and a secure administrator account for app configuration. If you plan to print badges, ensure you have a compatible printer connected or ready to pair via Bluetooth or USB. Finally, draft a simple privacy notice and a consent prompt to include in the sign-in flow, so visitors understand how their data will be used and stored.
Step-by-step: installing and configuring the app
Head to the App Store and install the chosen ipad visitor sign in app. Open the app and sign in with your admin credentials. Review and grant required permissions (Camera for QR codes, Local Network access for device discovery, Notifications for alerts). Create your first visitor sign-in template by naming fields and setting default values. Enable security features such as screen-lock and auto-logout after inactivity. Finally, test the setup on a secondary device to ensure the flow works as intended before going live.
Step-by-step: designing the visitor form
Designing a concise, privacy-friendly form is critical. Include fields for visitor name, host/escort, company, contact method, purpose of visit, and expected duration. Add optional fields sparingly (e.g., vehicle or appointment notes) and clearly state why data is collected. Use drop-downs or pre-filled options to reduce typing and errors. Publish consent language that explains data usage, retention, and who will access the information. This approach minimizes data collection while meeting operational needs.
Step-by-step: issuing badges and recording visits
Decide whether to print badges on check-in or display QR codes on-screen for later scanning. If printing, connect a compatible badge printer and define badge templates (visitor name, host, time-in, and expiry). For digital badges, ensure the QR code encodes a unique visit ID. The app should automatically save each check-in to a central log and push updates to connected systems. Verify that each sign-in creates a timestamp and attaches the visitor to the host for accountability.
Step-by-step: running sign-ins and exporting logs
During live sign-ins, guide visitors through the form with prompts and validation to reduce missing data. If the guest arrives without a prior appointment, allow a quick walk-in flow that still complies with privacy controls. When the session ends, export logs to a secure file or an integrated system for auditing. Schedule regular backups of sign-in data and practice data exports to ensure you can recover information if needed.
Data privacy, retention, and compliance considerations
Limit data collection to what is strictly necessary for safety and operations. Establish a data retention schedule and regularly purge records that exceed the permitted period. Use roles-based access so only authorized personnel can view or export logs. Provide visitors with a clear privacy notice and obtain consent when required by law. Consider regional privacy laws (e.g., general principles of data minimization and purpose limitation) and adjust your sign-in flow accordingly.
Troubleshooting common issues
If the app fails to load or signs in incorrectly, check network connectivity, verify that the device time is synchronized, and ensure the app is updated. For slow printing or badge generation, verify printer compatibility and driver settings. If logs do not sync, switch to offline mode and retry once the connection is restored. Review user permissions to confirm admins can access all required features.
Best practices for ongoing usage and maintenance
Schedule periodic reviews of field requirements, retention policies, and staff training. Run monthly tests of the sign-in flow to catch changes in hosts, locations, or access rules. Keep device firmware and app up to date, and establish a process for decommissioning old devices securely. Document incidents and improvements to demonstrate continuous security and usability enhancements.
Authoritative sources
- https://www.nist.gov/privacy
- https://www.usa.gov/privacy
- https://www.ed.gov
Tools & Materials
- iPad (latest model or compatible iPadOS version)(Ensure device is charged and updated to the supported iPadOS version)
- Charger and power backup(Keep a reliable power source for uninterrupted sign-in)
- Stable Wi-Fi or wired network(Reliable connectivity for real-time logging)
- Admin credentials for the sign-in app(Required for initial setup and configuration)
- Visitor badge printer (optional)(If badge printing is desired; ensure printer compatibility)
- Privacy notice template(Displayed within the form to inform visitors)
Steps
Estimated time: 60-90 minutes
- 1
Prepare the iPad
Charge the device fully, install the chosen sign-in app, and update to the latest supported iPadOS. Verify network access and confirm admin access for setup. This initial preparation prevents mid-session disruptions.
Tip: Test the device with a mock visitor to ensure the flow works before public use. - 2
Install and authorize the app
Download the app from the App Store, sign in with an admin account, and grant required permissions (Camera, Local Network, Notifications). This ensures features like QR codes and real-time alerts function correctly.
Tip: Enable two-factor authentication for admin accounts if available. - 3
Create a sign-in template
Set up the first visitor form, including name, host, company, contact method, purpose, and time-in/out. Keep defaults simple to minimize data entry during live sign-ins.
Tip: Use drop-down options to reduce errors and speed up check-ins. - 4
Configure privacy and consent
Add a short privacy notice and consent prompt. Clarify who can access the data and how long it will be stored. Compliance helps avoid misunderstandings and protects visitor rights.
Tip: Place consent before data submission to avoid friction at sign-in. - 5
Set up badges or QR codes
If printing, connect a badge printer and design a template with essential fields. If using digital badges, ensure the QR code encodes a unique visit ID for tracking.
Tip: Test scanning from multiple devices to ensure reliability. - 6
Enable check-in flow for guests
Publish the sign-in path for guests arriving without pre-scheduled visits. Include validation and host assignment to maintain accountability.
Tip: Provide a simple host lookup to quickly find the right escort. - 7
Configure logs export
Set export format (CSV or JSON) and destination (local storage, cloud, or integrated system). Ensure exports include timestamps and visit IDs.
Tip: Automate periodic exports to reduce manual work. - 8
Integrate with access controls
If your environment supports it, connect the sign-in app to door access or security systems to grant temporary permissions automatically.
Tip: Coordinate with security staff to align access rules. - 9
Establish data retention and roles
Define who can view, edit, or delete records. Set a retention window that complies with policy and legal requirements.
Tip: Review roles quarterly to ensure least privilege. - 10
Train staff
Provide onboarding for receptionists and hosts, including how to handle exceptions and privacy concerns. Practice with real visitors to reinforce learning.
Tip: Create a quick reference guide for common scenarios. - 11
Go live and monitor
Launch the system and monitor sign-in performance, host assignments, and data exports. Schedule periodic checks to catch issues early.
Tip: Log any incidents and iterate on the process based on feedback. - 12
Review and iterate
After the first month, review data quality, user feedback, and compliance posture. Adjust fields, prompts, and retention as needed.
Tip: Document improvements for future audits.
Questions & Answers
What data should I collect on a visitor form?
Collect only essential details such as name, host, company, contact method, and purpose of visit. Avoid storing sensitive information unless required by policy, and provide a clear privacy notice.
Collect only the essentials, and always provide a privacy notice before data entry.
Can I customize the sign-in flow for different visitor types?
Yes. Most apps let you tailor forms by visitor type (delivery, guest, contractor) and adjust fields accordingly to streamline the experience.
Yes, you can tailor the form for different visitor types.
Is this approach compliant with privacy laws?
Follow local data protection laws by limiting data collection, obtaining consent where required, and retaining records only as long as needed.
Follow local privacy laws and keep data only as long as needed.
What should I do if the app cannot sync logs offline?
Use offline mode to capture data, then retry syncing when the network is restored. Check for updates if syncing problems persist.
If offline, store locally and sync later when online.
Can I export check-in logs to another system?
Yes. Most apps support exporting to CSV or JSON or offer integration hooks with security or access-control systems.
You can export logs to CSV/JSON or integrate with other systems.
How often should I review sign-in data?
Review at least monthly to ensure data quality, privacy compliance, and that retention policies are followed.
Review data monthly to maintain quality and compliance.
Watch Video
Highlights
- Start with a privacy-first sign-in design
- Choose features that fit your facility’s workflow
- Test thoroughly before going live
- Protect visitor data with roles and retention policies
- Use exports to support audits and reporting